Connectors
Connect your cloud accounts, SaaS platforms, and developer tooling to AiVRIC CloudSignals+RiskOps™. Each connector uses read-only credentials — AiVRIC never requires write access for monitoring. Once connected, an automated audit runs every 24 hours to detect misconfigurations and posture drift.
Amazon Web Services
Cloud ProviderSecurely connect your AWS accounts for continuous compliance monitoring and telemetry ingestion. AiVRIC performs an agentless read-only audit every 24 hours.
- AWS Account ID: Found in the top-right dropdown of the AWS Console.
- STS active: Confirm your AWS Security Token Service (STS) has the EU (Ireland) endpoint active to allow the cross-account connection.
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select Amazon Web Services.
Enter your AWS Account ID
Enter your 12-digit AWS Account ID and provide a friendly alias to identify this environment in your dashboard (e.g., prod-us-east).
Choose authentication method
AiVRIC supports two authentication methods:
| Method | Recommended use | Security level |
|---|---|---|
| AWS SDK Default (IAM Role) | Long-term production | High — role-based, no static keys |
| Access & Secret Key | Quick / one-time scans | Low — static keys, not for production |
Recommended: Select Connect assuming IAM Role. Use the AWS CloudFormation Quick Link in the dashboard to automatically provision the read-only IAM role. Paste the generated Role ARN and confirm the External ID matches the value shown in AiVRIC.
Verify and launch scan
Review your connection details, then click Launch Scan. AiVRIC will immediately perform a baseline audit and continue automatically every 24 hours. To run a single audit without enabling the recurring schedule, select Run a single scan before clicking Launch.
Microsoft Azure
Cloud ProviderConnect your Azure subscriptions for continuous compliance and secure telemetry ingestion. AiVRIC uses a Service Principal with scoped read-only permissions.
- Subscription ID: Your unique Azure subscription identifier (found in the Azure Portal under Subscriptions).
- Service Principal: An Entra ID App Registration with Reader or Security Auditor role assigned at the subscription scope. See the Service Principal setup guide below if you haven't created one yet.
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select Microsoft Azure.
Enter your Subscription ID
Paste your Subscription ID from the Azure Portal. Optionally add a friendly alias (e.g., azure-prod).
Enter Service Principal credentials
Provide the following from your Entra ID App Registration:
- Client ID: The Application (client) ID from the App Registration overview.
- Client Secret: The secret value generated under Certificates & secrets. Copy it immediately — Azure hides it after you leave the page.
- Tenant ID: The Directory (tenant) ID from the App Registration overview.
Verify and launch scan
Once credentials are accepted, click Launch Scan. AiVRIC will run the baseline audit immediately and then every 24 hours thereafter. Select Run a single scan to disable the recurring schedule.
Azure Service Principal setup
If you need to create a Service Principal for AiVRIC, follow these steps in the Azure Portal:
- Go to Microsoft Entra ID > App registrations and click + New registration. Name it
AiVRIC-Scannerand click Register. - On the Overview page, copy the Application (client) ID and Directory (tenant) ID.
- Go to Certificates & secrets, click + New client secret, and copy the Secret Value before leaving the page.
- Search for Subscriptions, select your target subscription, and copy the Subscription ID.
- Under Access Control (IAM), click + Add role assignment. Assign the Reader or Security Auditor role to the
AiVRIC-Scannerapp registration.
Return to the AiVRIC onboarding flow with these four values: Tenant ID, Client ID, Client Secret, and Subscription ID.
Google Cloud Platform
Cloud ProviderConnect your GCP projects for continuous compliance monitoring and automated risk scoring. AiVRIC uses a Service Account Key with read-only permissions.
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select Google Cloud Platform.
Enter your GCP Project ID
Enter your unique GCP Project ID for the project you want to audit. Optionally add a friendly alias.
Choose authentication method
Select Connect via Service Account Key. In the GCP Console, create a Service Account with the Security Reviewer and Viewer roles, generate a JSON key, and paste the full contents of the key file into the field provided in AiVRIC.
Verify and launch scan
Click Launch Scan to begin. AiVRIC will run a baseline audit immediately and then every 24 hours. Use Run a single scan for a one-time assessment.
Kubernetes
Container PlatformGain unified visibility and posture monitoring across your containerized environments — including EKS, GKE, AKS, and self-managed clusters.
- Kubeconfig file: Locate it at
~/.kube/configon your management machine. - Managed clusters (EKS/GKE/AKS): Ensure the cluster allows inbound API traffic from AiVRIC and that you have applied the required RBAC resources (ServiceAccount, ClusterRole, ClusterRoleBinding) with read-only permissions.
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select Kubernetes.
Enter cluster context
Identify the Kubernetes cluster context from your kubeconfig file (the value under contexts[].name) and enter it in the Cluster Context field.
Provide kubeconfig
Paste the full contents of your kubeconfig YAML into the authentication field. AiVRIC uses this to authenticate and enumerate cluster resources with read-only access.
Verify and launch scan
Review the connection summary and click Launch Scan. AiVRIC will run an automated audit every 24 hours to ensure continuous compliance across your cluster workloads.
GitHub
Developer PlatformSecure your repositories and delivery workflows with continuous monitoring of branch protections, secret exposure, repository settings, and pipeline configurations.
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select GitHub.
Enter GitHub account details
Provide your GitHub Username or Organization name. Add a friendly alias to distinguish this account in your dashboard.
Choose authentication method
Select one of three options:
- Personal Access Token (PAT): Generate a fine-grained PAT in GitHub with read-only repo and org scopes.
- OAuth App Token: Authorize via the AiVRIC OAuth app for your GitHub org.
- GitHub App: Install the AiVRIC GitHub App for least-privilege, per-repo access.
Enter the required token or complete the OAuth flow to establish the secure connection.
Verify and launch scan
After a successful connection test, click Launch Scan. AiVRIC will automatically scan every 24 hours to detect repository misconfigurations and risks.
Microsoft 365
SaaS PlatformConnect your Microsoft 365 tenant for continuous compliance monitoring and agentic security intelligence. CloudSignals+RiskOps™ will continuously map your tenant controls to frameworks including SOC 2 and PCI DSS.
- App Registration: Register a new application in Microsoft Entra ID (see Step 3 for details).
- API Permissions: Grant the required Microsoft Graph and external API permissions to the app registration.
- PowerShell 7.4+: Required on the scanning host to enable full M365 check coverage (particularly PowerShell-based auditing for Exchange and Teams).
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select Microsoft 365.
Enter your Domain ID
In your Entra ID portal, locate the domain that acts as the unique identifier for your account (e.g., contoso.onmicrosoft.com). Paste this into the Domain ID field in AiVRIC.
Set up Certificate Authentication (recommended)
- Generate certificate: Create a self-signed certificate and export it as a Base64-encoded PFX file. Example using PowerShell:
$cert = New-SelfSignedCertificate -Subject "AiVRIC-Scanner" -CertStoreLocation "Cert:\CurrentUser\My"
Export-PfxCertificate -Cert $cert -FilePath "aivric-scanner.pfx" -Password (Read-Host -AsSecureString) - Upload to Azure: Export the public portion (
.cer) and upload it to your Entra ID App Registration under Certificates & secrets. - Configure AiVRIC: Select Certificate (Recommended) in the AiVRIC onboarding screen.
- Provide IDs: Enter your Tenant ID and Application (Client) ID from the App Registration overview.
- Upload PFX: Upload the PFX certificate file directly into the AiVRIC platform.
Verify and launch scan
Review the summary and click Launch Scan. AiVRIC will perform a baseline audit and then automatically scan every 24 hours to detect drift and misconfigurations across your tenant. Compliance evidence is captured continuously and mapped to SOC 2, PCI DSS, and CMMC frameworks automatically.
MongoDB Atlas
Database PlatformConnect your MongoDB Atlas organization for continuous security monitoring and risk intelligence across your database clusters and projects.
- API Key Pair: Generate an API key in the MongoDB Atlas Console under Organization Settings > Access Manager > API Keys.
- Note the Public Key (your API identifier) and the Private Key (the corresponding secret). The private key is only shown once at creation time.
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select MongoDB Atlas.
Provide API key credentials
Paste your Public Key and Private Key into the required fields. AiVRIC uses the API key pair to authenticate with the Atlas API and enumerate your organization's configuration.
Verify and launch scan
After the platform verifies the connection, click Launch Scan. AiVRIC will automatically run a scan every 24 hours to detect misconfigurations and security drift across your Atlas clusters.
Alibaba Cloud
Cloud ProviderConnect your Alibaba Cloud account for continuous compliance monitoring and risk intelligence. AiVRIC supports RAM Role Assumption for secure, long-term production use.
- Account ID: Click your profile avatar in the top-right corner of the Alibaba Cloud Console to find your Account ID.
- Permissions: Ensure you have a RAM User with Access Keys, or a RAM Role with read-only permissions (ReadOnlyAccess policy recommended) sufficient to audit your resources.
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select Alibaba Cloud.
Enter your Alibaba Cloud Account ID
Enter your Alibaba Cloud Account ID and optionally a friendly alias to identify this account in the dashboard.
Choose authentication method
AiVRIC supports two methods:
| Method | Best for | Security level |
|---|---|---|
| RAM Role Assumption | Long-term production | High — secure cross-account access |
| Static Credentials (Access Key ID + Secret) | Quick / one-time scans | Low — avoid for production |
Recommended: Select RAM Role Assumption. Provide the Role ARN and the Access Key ID / Secret of the RAM user authorized to assume that role. For static credential scans, enter the Access Key ID and Secret directly.
Verify and launch scan
Review your configuration, then click Launch Scan. AiVRIC will automatically run a scan every 24 hours to detect misconfigurations and posture drift.
Cloudflare
Network & Security PlatformConnect your Cloudflare account to monitor DNS security, WAF rule posture, Zero Trust access policies, firewall rules, and account-level configuration drift across your zones and teams.
- API Token: Create a scoped API token in the Cloudflare dashboard under My Profile > API Tokens. Use the Read All Resources template or create a custom token with the permissions listed below.
- Required permissions (read-only): Account Settings: Read; Zone Settings: Read; Firewall Services: Read; Access: Apps and Policies: Read; DNS: Read.
- Account ID: Found in the Cloudflare dashboard right sidebar on any zone overview page.
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select Cloudflare.
Enter your Account ID
Paste your Cloudflare Account ID and optionally add a friendly alias to identify this account in the dashboard (e.g., cloudflare-prod).
Provide your API Token
Paste the scoped API Token generated in the Cloudflare dashboard. AiVRIC uses this token to authenticate against the Cloudflare API with read-only access to your account, zones, firewall rules, Zero Trust policies, and DNS records.
| Coverage area | What AiVRIC audits |
|---|---|
| Zones & DNS | DNSSEC status, proxy mode, record hygiene, TTL anomalies. |
| WAF & Firewall | Managed ruleset version, custom rule gaps, rate limiting posture. |
| Zero Trust | Access application policies, identity provider bindings, device posture rules. |
| Account settings | Two-factor enforcement, audit log configuration, API token hygiene. |
Verify and launch scan
Click Launch Scan to begin. AiVRIC will run a baseline audit immediately and then automatically every 24 hours to detect firewall misconfigurations, policy drift, and security posture changes across your Cloudflare account.
OpenStack
Private Cloud PlatformConnect your OpenStack deployment for continuous posture monitoring of compute, network, identity, and storage services across your private cloud infrastructure.
- Keystone endpoint: The public or internal Keystone Identity API endpoint for your OpenStack deployment (e.g.,
https://keystone.example.com:5000/v3). - Application credential or service account: AiVRIC recommends using an Application Credential (Keystone v3) scoped to the target project with a read-only role (reader or equivalent). Avoid using admin credentials.
- Project/Tenant ID: The UUID of the OpenStack project you want to audit.
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select OpenStack.
Enter your Keystone endpoint and Project ID
Provide the Keystone Identity API URL and the Project ID for the project you want to audit. Optionally add a friendly alias (e.g., openstack-dc1).
Choose authentication method
AiVRIC supports two authentication approaches:
| Method | Best for | Security level |
|---|---|---|
| Application Credential | Long-term production | High — project-scoped, no admin exposure |
| Username / Password + Domain | Quick assessments | Medium — avoid admin accounts |
Recommended: Use an Application Credential. In Horizon or via the OpenStack CLI, create an application credential scoped to your target project with the reader role. Paste the Credential ID and Credential Secret into AiVRIC.
For username/password auth, provide the Username, Password, User Domain Name, and Project Domain Name.
Verify and launch scan
Click Launch Scan. AiVRIC will connect to your OpenStack APIs (Nova, Neutron, Keystone, Cinder, Swift) and run a baseline posture audit immediately, then every 24 hours to detect drift across your private cloud resources.
Oracle Cloud Infrastructure
Cloud ProviderConnect your OCI tenancy for continuous posture monitoring across compute, networking, identity, storage, and security services. AiVRIC uses a dedicated IAM user with read-only policy permissions — no instance principal or admin credentials required.
- Tenancy OCID: Found in the OCI Console under Profile > Tenancy.
- User OCID: Create a dedicated IAM user (e.g.,
aivric-scanner) in Identity > Users and copy its OCID. Assign a group with the ReadOnlyAccess or equivalent read-only policy at the tenancy or compartment scope. - API signing key: Generate an RSA key pair (2048-bit minimum). Upload the public key to the IAM user's API Keys section and retain the private key for the connection.
- Fingerprint: Shown in the OCI Console after uploading the public key.
- Region: The OCI region identifier for your home region (e.g.,
us-ashburn-1).
Navigate to Cloud Providers
In the AiVRIC sidebar, go to Settings > Cloud Providers. Click Add Cloud Provider and select Oracle Cloud Infrastructure.
Enter tenancy details
Provide your Tenancy OCID, User OCID, and the OCI Region identifier. Optionally add a friendly alias (e.g., oci-prod-ashburn). To scope monitoring to a specific compartment rather than the full tenancy, enter the Compartment OCID as well.
Configure API key authentication
OCI uses RSA key-pair signing for API authentication. Paste the contents of your private key (PEM format) and the corresponding Key Fingerprint shown in the OCI Console after you uploaded the public key to the IAM user.
| Coverage area | What AiVRIC audits |
|---|---|
| Identity & Access (IAM) | User MFA status, policy permissiveness, API key rotation age, group membership hygiene. |
| Compute (Instances) | Unencrypted boot volumes, public instance exposure, metadata service configuration. |
| Networking (VCN) | Security list rules, open ingress/egress, subnet routing anomalies, internet gateway exposure. |
| Storage (Object & Block) | Public bucket access, encryption enforcement, lifecycle policy gaps. |
| Security Services | Cloud Guard status, Vulnerability Scanning configuration, audit log enablement. |
| Database | Autonomous DB network access controls, encryption configuration, backup policy. |
Verify and launch scan
Click Launch Scan. AiVRIC will validate the API key against your tenancy and run a baseline posture audit immediately, then every 24 hours to continuously detect drift across your OCI resources. Select Run a single scan to perform a one-off assessment without enabling the recurring schedule.
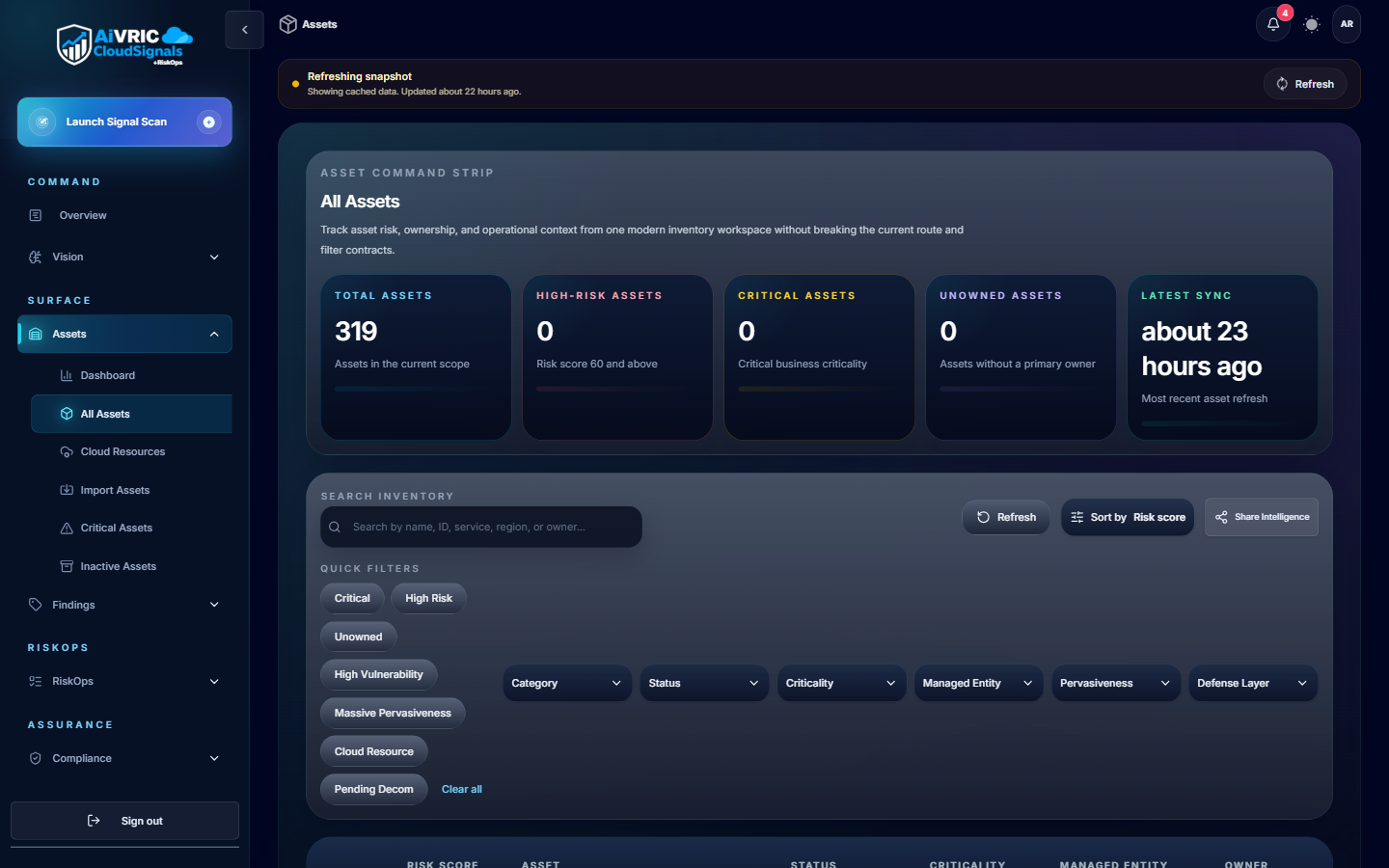
After connecting
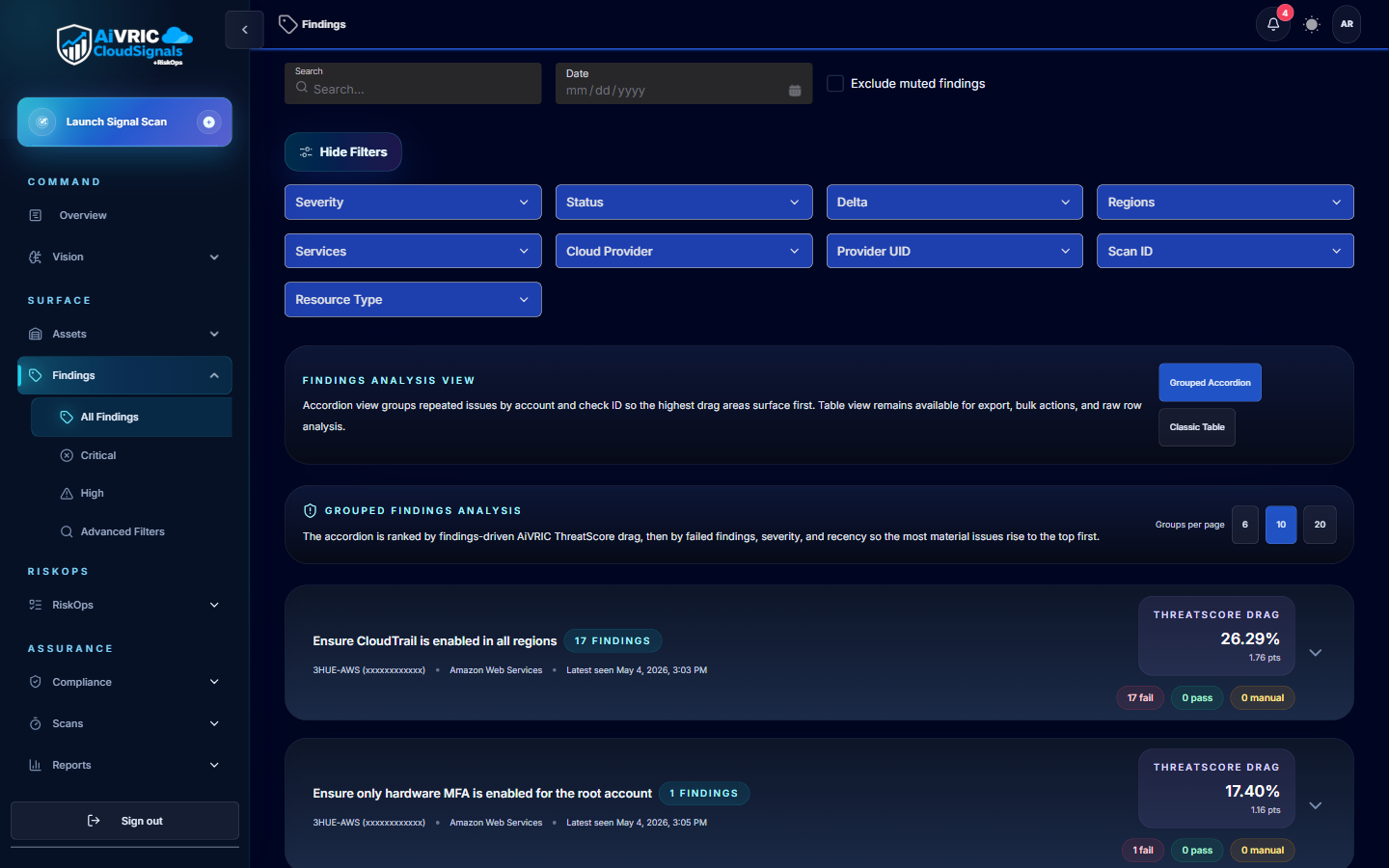
Review your first findings
Navigate to the Findings panel. Filter by severity and assign owners. Critical and High findings surface at the top with AI-driven remediation steps.
Enable compliance frameworks
In Settings > Policy Packs, enable SOC 2, PCI DSS, or ISO 27001 mapping. CloudSignals+RiskOps will immediately re-score your posture against the selected framework.
Set up notifications
Configure Slack, Teams, Jira, or ServiceNow alerts in Settings > Notifications. Route Critical findings to your on-call channel for rapid response.
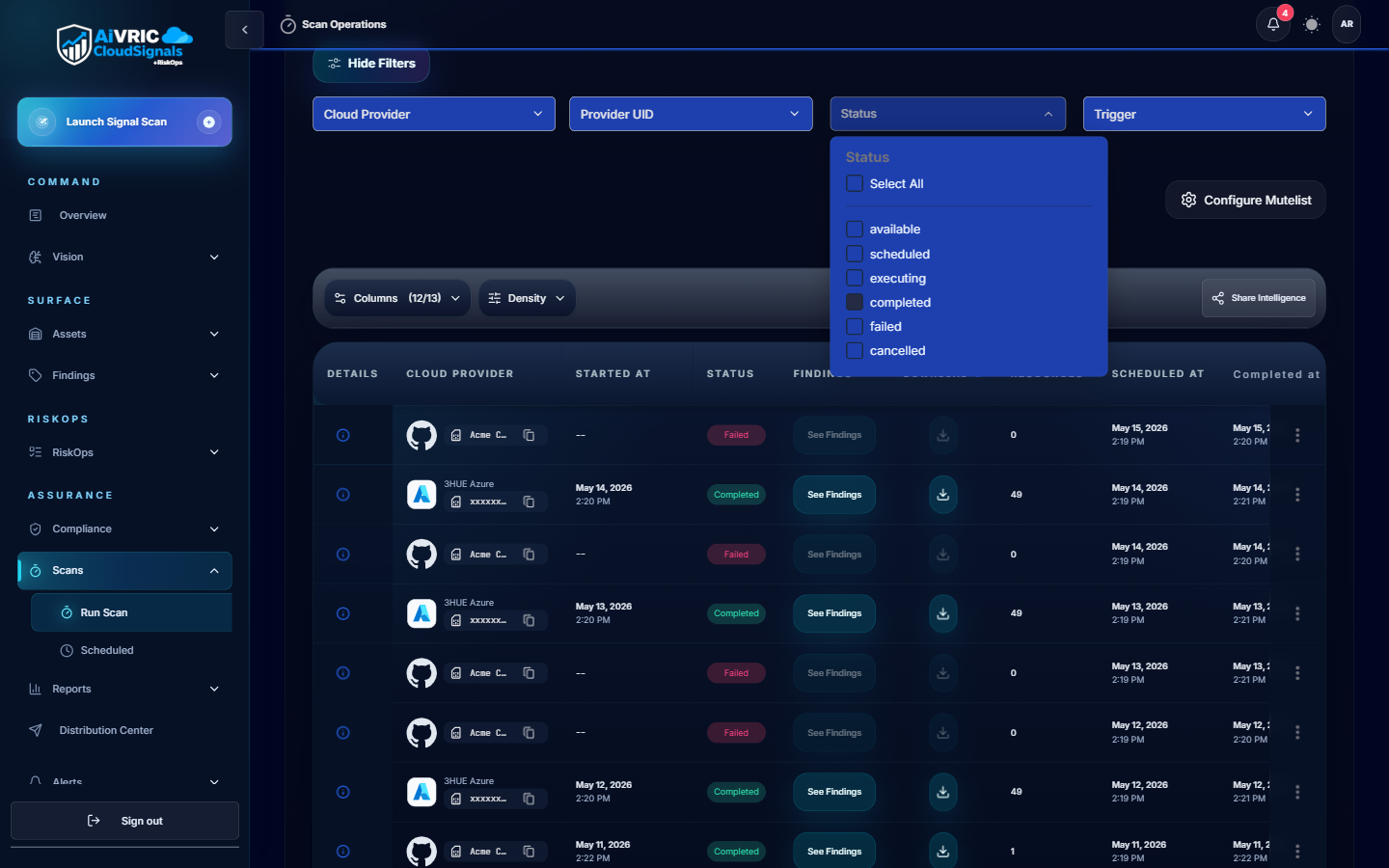
Schedule scan windows
Adjust the 24-hour scan cadence in Settings > Scheduling & Scan Windows to avoid peak-traffic periods or align with your change-freeze policies.
